TechEd North America 2014, Houston
Data Privacy and Protection in the Cloud– A.J. Schwab, Jules Cohen, Sarah Fender
Day 2, 13 May 2014, 10:15AM-11:30AM (OFC-B233)
Disclaimer: This post contains my own thoughts and notes based on attending TechEd North America 2014 presentations. Some content maps directly to what was originally presented. Other content is paraphrased or represents my own thoughts and opinions and should not be construed as reflecting the opinion of either Microsoft, the presenters or the speakers.
Executive Summary—Sean’s takeaways
-
The issue of Trust is important whenever you talk about moving data to cloud
- Need to convince users that data will be secure, private
- Need to convince users that data will be secure, private
- Data Privacy is key goal for Microsoft
- Lots of tools for controlling access to data, e.g. identity management
-
Security at many layers, e.g. physical, network, etc.
- Microsoft pours lots of resources into security for the layers that they control
Jules Cohen – Trustworthy Computing group, Microsoft
Three major buckets, when thinking about moving data to the cloud
- Innovation properties – will cloud let me do what I want?
- Economics – what is TCO?
- Trust
First two buckets are relatively un-complicated
- Trust – harder to evaluate, more visceral
- Privacy and data protection are part of trust
Trust
- Microsoft has made significant investments
- If you already trust the cloud, we’re going to improve level of trust
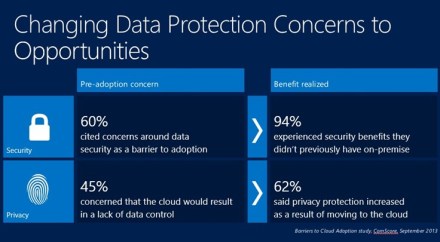
Changing Data Protection concerns to opportunities
- You already trust people within your organization
- In cloud world, some of these functions move off premises
-
Ref: Barriers to Cloud Adoption study, ComScore, Sept-2013
- 60% – security is barrier to cloud adoption
- 45% – concerned about data protection (privacy)
Definitions
- Can’t have privacy without security
-
Security is a pre-req
- Do the right people have access to the data?
-
Once data is in the right hands, we can talk about privacy
- Do people who have access to data use it for the right things?
Perceptions after migration to cloud
- 94% – said they experienced security that they didn’t have on-premise
- 62% – said privacy protection increased after moving to cloud
Microsoft’s approach to data protection
-
1 – Design for privacy
- Corporate privacy policies, disclosures
- Trustworthy Computing formed in 2002, after memo from Bill Gates—privacy, security, reliability
-
2 – Built-in features
- Customers can use these features to protect their data
-
3 – Protect data in operations
- Operating services – Microsoft committed to data protection in service operations
- Microsoft complies with various standards, help customers comply with those standards
- 4 – Provide transparency and choice
Privacy governance – Program
- Design for Privacy
- People – Employee several hundred people focused on privacy
-
Process
- Internal standards
- Rules maintained by Trustworthy Computing
-
Technology
- Use tools to support people and processes
- Look for vulnerabilities
Privacy government – Commitments
- Microsoft services meet highest standards in EU (Article 29)
- First (and only) service provider to get this approval
Sarah Fender – Director of Product Marketing, Windows Azure, Microsoft – Built-in Features

Data Protections in Azure
- Data location – can choose to run in a single region, or multiple regions
-
Redundancy & Backup
- 3 copies of data, within region
- Can also do geo-redundant storage, to different region
- E.g. Create new storage account, pick region
-
Manage identities and access to cloud applications
- Centrally manage user accounts in cloud
- Enable single sign-on across Microsoft online service and other cloud applications
- Extend/synchronize on-premise to cloud – Active Directory synching to Azure
-
Monitor and protect access to enterprise apps
- Passwords stored in encrypted hashes
- Security reporting that tracks inconsistent access patterns – e.g. user accessing service from distant geo-locations
- Step up to Multi-Factor Authentication – e.g. text message or e-mail with secret code


Data encryption
- VMs – encrypted disk using BitLocker
- Can encrypt data at rest
- SQL TDE
- Applications – RMS SDK
- Storage – .NET Crypto, BitLocker (import/export), StorSimple w/AES 256
Data protections in Office 365
- Encrypt data in motion and also at rest

A.J. Schwab – Senior Privacy Architect, Office 365, Microsoft – Protect Data in Operations
Value proposition of running in cloud
- Less work—patching, reacting to problems
Defense in depth strategy
-
Physical
- Who comes into facility?
- What media goes in/out?
- If bad guy can stand in front of your computer, it’s not your computer anymore
-
Network
- Looking for anomalous traffic
- Packet penetration testing
- Watching logs
-
Identity & Access Management
- Internal Microsoft authentication policies for internal staff
- Know who people are and who gets access from within Microsoft
- Just-in-time access – when someone wants access to customer information, it’s an exception
-
Host Security
- Patching, managing OS on host
-
Application
- Make sure that application is running in secure configuration
-
Data
- “Data is everything” – data is money
- Big part of the focus, protesting the data
- 24x7x365 incident response

Cloud security must be equal or better to on-premise
Protect data in operations
-
Data isolation
- Very important to customers
- Only privileged user has access to data
-
Limited Access
- MFA for service access
- Auditing of operator access/actions
- Zero standing permissions in the service
-
Automatic Microsoft staff account deletion
- To make sure that things follow policies, everything is automated
-
Staff background checks, training
- Can Microsoft trust the people that it hires?
Approach to Compliance
- Industry standards and regulations
- Controls Framework & Predictable audit schedule
- Certification and Attestations
Customer Stories – Kindred Healthcare
-
Background
- Big healthcare provider
- Mobile service, ensure data privacy
-
Solution
- Office 365 Exchange, SharePoint, Lync
- Met security and privacy needs
Shared Protection Responsibility
- IaaS – cloud customer has most of the responsibility
- SaaS – cloud provider assume many of the responsibilities
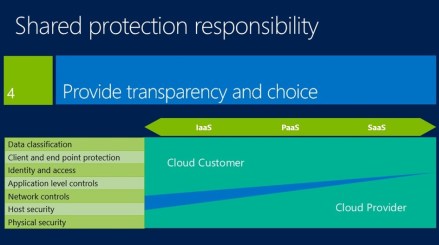
Provide transparency and choice
- Trust Center web page – for Office 365, and for Azure
- Lots of documentation online
Summary
- 1 – Design for privacy
- 2 – Built-in features
- 3 – Protect data in operations
- 4 – Provide transparency and choice
Questions and Answers
Q: Sharepoint, is data encrypted while data is at rest? Is BitLocker available? Or third-party products?
- Microsoft has committed to goal of having all data in transit and all data at rest is encrypted
- By the end of 2014, Sharepoint data at rest will be fully encrypted
- But law enforcement has generally been satisfied with current security and privacy policies
Q: What tools do you have to assist attorneys?
- See materials in the Trust Center
- Microsoft constantly talking to lawyers, to stay on top of current regulations
- So probably collateral materials that are required are there
- We do have Controls Framework that maps what Microsoft does and maps it to specific regulatory requirements
- Thinking about how to package this up and present it for customers
Q: How to evaluate tools based on legal requirements?
- We (Microsoft) can’t give you (customer) legal advice. But we can show you how tools map to particular requirements
- Can do this in the context of certain verticals, e.g. Banking
If you have questions, stop by the Security & Compliance station in the Azure booth